E-commerce
March 25, 2025
Marketing, support, logistics, finance: the larger your team grows, the more Shopify admin concentrates sensitive actions (orders, customers, payments, apps). The roles and permissions make it possible to apply the principle of least privilege without micro-managing every checkbox for each person. This guide is based on the official documentation: User management, Permissions, Role management, Sensitive permissions, the security settings, and the OWASP Authorization Cheat Sheet for the “who can do what” framework on the application security side. For another step-by-step angle, see also RBAC in Shopify admin.
The goal is not to cite global average breach costs: it is to structure access, document roles, and review permissions when the organization changes.
Summary
RBAC and Shopify terminology
The role-based access control (RBAC) groups permissions into reusable roles. In Shopify, a role has a name, a description, and a set of permissions; you then assign it to the accounts that need it. The user management section indicates that roles and permissions are used to grant the necessary level of access while limiting what is not essential to the work.
“Permissions grant or restrict access to specific areas of your business for a given context. You can assign permissions to roles to give a user granular levels of access based on the role category.”
Shopify Help Center, Permissions page (free translation and quotation)
Common entry point: Settings > Users > Users and Roles tabs, depending on whether your context is store-only or organization. The exact interface may vary if you are in a multi-store organization.
RBAC does not replace the internal security policy: it operationalizes it. As soon as more than one person logs in to the admin, set rules for shared accounts (to be avoided except in documented exceptional cases), password rotation for technical accounts, and the use of named accounts for any traceable action on orders or customer data.
Types of permissions: store, organization, POS
Shopify distinguishes several families of permissions:
Store: for roles in the « Store Role » category.
Organization: for roles in the « Organization Role » category (multi-store context).
Shopify POS: for POS roles when the point of sale is used.
Some tasks (detailed user and role management) are not exposed as simple checkboxes: they are reserved for authorized profiles, as explained in the user management requirements.
Role categories and packages
The Role management page notes that the available role types depend on the plan, membership in an organization, Shopify Plus for some custom organization roles, and the presence of POS Pro for POS roles. The roles managed by Shopify are not editable: you duplicate or create custom roles alongside them.
Question | Answer clue |
|---|---|
Can I create roles on Basic or Starter? | The docs tie store custom roles to plans beyond Basic/Starter; check your screen and the updated help page. |
Plus and organization | Custom organization roles mainly apply in the Plus and multi-store context. |
POS | POS roles and POS employees if the POS channel + location has POS Pro. |
Sensitive permissions and customer data
Sensitive permissions give access to private data: finances, billing payment methods, customer data requests, or sensitive information about a business entity in the organization. Granting them makes it possible to delegate workflows (e.g. GDPR-related aspects or payment settings) while distributing tasks among several people rather than concentrating all access in a single account.
From a compliance perspective, link each sensitive permission to an internal procedure: who can approve an export, who can modify a payment method, and how you record the action in your tools (tickets, internal notes). The CNIL website reminds us of individuals' rights over their data: your roles must be consistent with who is authorized to respond to requests.
Create, duplicate, and edit a role
Creation follows the documented path: Settings > Users > Roles > Add a role, choose the category, name, description, then select permissions and, optionally, accessible apps. The duplication copies an existing role not managed by Shopify to speed up a neighboring role (e.g., “Support Level 1” from “Support Level 2” with fewer checkboxes).
If you need to change a role category afterward, the documentation indicates that you must create a new role: the category cannot be changed after creation. Plan on stable naming (support_tier1_v2 internal) to avoid a proliferation of dead roles.
Assigning roles and multi-store access
The Roles management page explicitly states that one or more roles can be assigned to a user (or a POS staff member), in order to fine-tune permissions uniformly and limit accidental access. For organizations, you can then adjust the stores the user has access to after assigning a store role.
In practice, avoid stacking roles without a clear map: each combination should correspond to a job title or a named use case, otherwise audits become opaque.
POS roles and in-store staff
If you sell in-store, POS permissions determine what staff can do at checkout: discounts, refunds, opening the cash drawer, reports. They depend on the presence of the POS sales channel and POS Pro at at least one location, as noted in the section on eligibility criteria. Align POS roles with your anti-fraud procedures: separate the person who approves a large refund from the one who rings up sales that same day, even if the tool allows it.
Employee and partner accounts
Collaborator accounts allow Shopify partners to work on your store with controlled permissions. Distinguish them from internal staff accounts: governance (who invites whom, duration, app scope) should be just as clear as for an employee.
For each contractor, list the relevant apps, topic-based access (theme, catalog, billing), and the end date of the engagement. When the project ends, revoke collaborator access before closing the contract: too long a delay between the end of the engagement and deactivation is a frequent source of unnecessary exposure.
User groups
Shopify also lets you structure users through groups in contexts where this feature is available. Groups complement roles when you need to apply common policies to entire teams (for example, access to a set of stores or organization segments). Check in your admin whether your plan and structure expose groups: the interface evolves with organization and Plus plans.
In practice, a group can serve as an HR “tag” for auditing: “all employees of the Lyon store” without replacing the job role that defines fine-grained permissions. Avoid multiplying groups that duplicate roles: keep a simple rule, for example role = permissions, group = organizational scope.
Permissions and Settings page
Certain actions in Settings (billing, payment methods, users) require specific permissions. The page on the permissions required for options on the Settings page details these dependencies: useful when a team member sees a grayed-out menu without understanding why. If blocked, start by checking the role, then the sensitive permissions, then membership in a multi-store organization.
Document internally who can invite new users: on non-Plus stores, the documentation often restricts user management to the owner and store admins; in an organization, other organization roles may come into play. Refer to the tables on the user management requirements page for your case.
Invitations, CSV export and reviews
The user invitation process should be standardized: work email, the name of the assigned role before sending, and verification that the employee has accepted the invitation. Pending accounts represent a risk if the email was entered incorrectly: a misspelled domain sends an invitation outside the organization.
When your organization allows it, the CSV export of user management information makes periodic reviews easier: cross-check the list with your HR directory to identify orphaned accounts. Schedule a quarterly review of roles: teams change faster than internal documentation.
Least privilege, audit, and 2FA
OWASP recommends designing systems where users obtain only the rights necessary for their role and regularly reviewing these rights. This is the spirit of the Authorization Cheat Sheet, adaptable to your Shopify matrix: fewer "store admin" accounts on a daily basis, more explicit business roles.
Shopify also ties sensitive permissions to trust in the two-factor authentication: the page on sensitive permissions mentions the value of 2FA in reducing risk on accounts that handle critical data. Require 2FA for owners and administrators, and train teams on phishing targeted at e-commerce access.
Examples of matrices by profession
The tables below are starting templates: adapt them to your plan, your apps, and your legal requirements.
Job role | Typical permissions | Avoid |
|---|---|---|
Customer support | Orders (view, edit), customers, creation of purchase orders | Global payment settings without need |
Logistics | Orders (fulfillment), products (view), inventory | Deleting apps or billing |
Content marketing | Products, collections, content, campaigns as needed | Mass export of customer data without a framework |
For detailed catalog operations, keep the link with adding products and data quality rules.
Finance teams often need to export reports without modifying payment methods: separate « view payments » and « edit billing settings » when the interface allows it, rather than giving a full admin role. Legal / compliance teams may require permissions related to customer data requests: tie this scope to your records of processing activities and your internal GDPR procedures.
Third-party apps and access scope
When creating or editing a role, the App permissions section makes it possible to limit which apps a user sees in the admin. This is useful when a team uses only an email tool or an ERP connector: reducing the list limits the risk of mistakes and clarifies the interface. Cross-check this with your app purchasing policy: each new installation should not imply « full access for everyone » by default.
Apps can also request broad API scopes on the developer side: from a governance perspective, keep a list of approved integrations and disable staff access to outdated apps when you switch tools. For an overview of integrations, see Shopify integrations.
Common mistakes
Error | Risk | Remediation |
|---|---|---|
Too many "administrator" profiles | Large attack surface | Documented intermediate roles |
Duplicated roles without maintenance | Outdated permissions | Quarterly review, removal of unused roles |
Forgetting to revoke access when someone leaves | Orphaned accounts | Offboarding checklist + deactivation |
Partners with too broad a scope | Prolonged exposure | Time-limited collaborator, limited by app |
Quick checklist when a team member arrives
Define the role or combination of roles before the invitation.
Invite the user and verify access to the correct stores.
Validate a test action (view an order, adjust inventory) within the planned scope.
Document the assignment in your internal HR / IT repository.
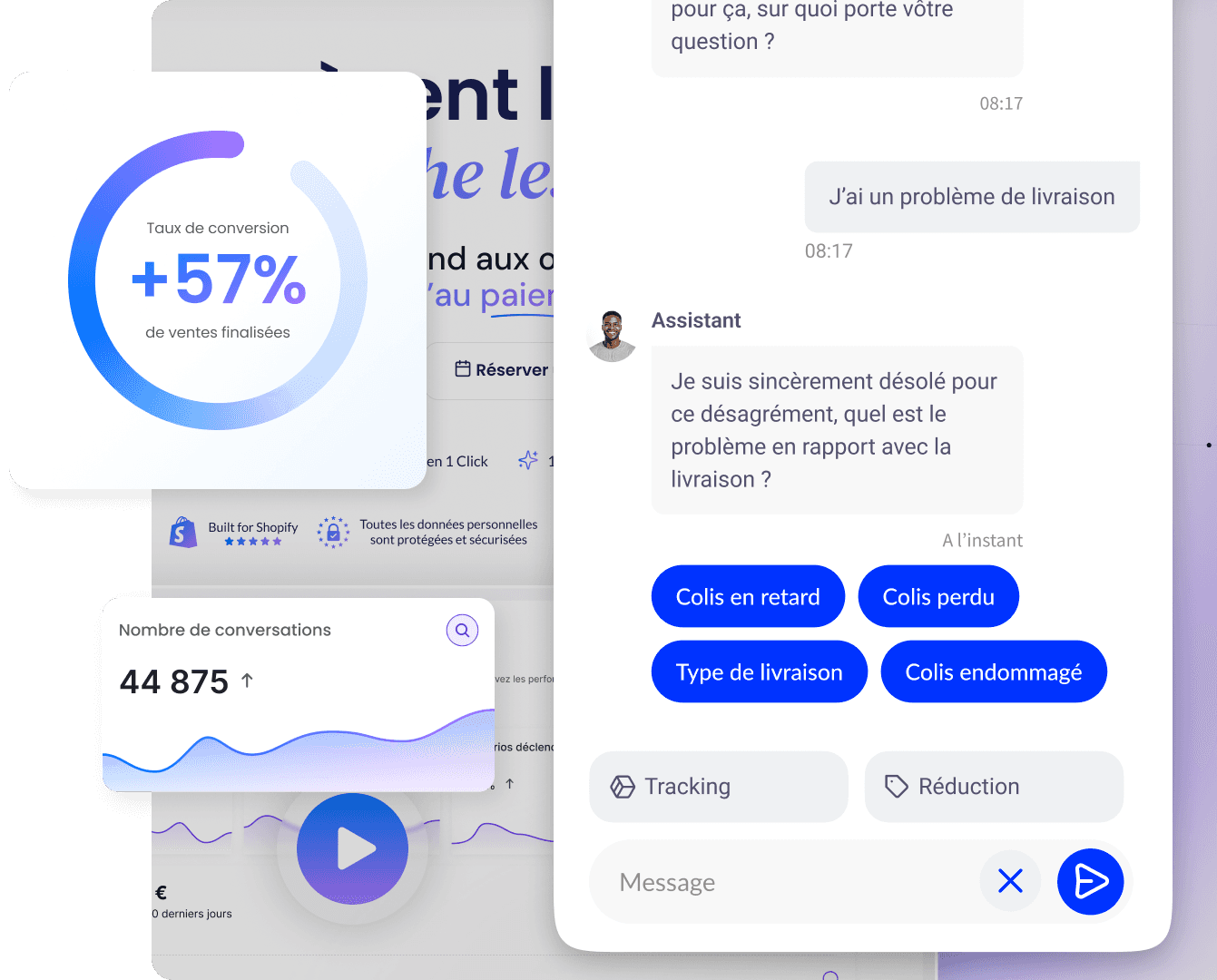
Chatbot and exposure surface
A chatbot like Qstomy handles visitor questions on the public store: it does not replace staff account governance, but it reduces the need to give admin access to teams that only needed access to FAQ answers. Fewer sensitive accounts, less risk, provided the bot is kept up to date with your policies.
Summary
Role-based access controls in Shopify rely on permissions grouped into customizable roles, with different rules depending on plan, organization, Plus, and POS. Identify sensitive permissions, limit high-privilege accounts, duplicate roles to iterate quickly, and review combinations when team changes occur. Rely on Shopify documentation and OWASP best practices to structure your access reviews.
Also think about external collaborators, user exports, and apps: each access channel should have an owner and a review date. A clean admin reduces human errors on orders and customer data, and makes team growth easier without multiplying default "super-admin" accounts.
FAQ
Can a user have multiple roles?
Yes. The documentation on role management indicates that one or more roles can be assigned to the same user in order to refine permissions consistently.
How many custom roles can I create?
It depends on your plan and the limits shown in admin; also check the page maximum number of users per plan.
Can I modify a Shopify-managed role?
No. Shopify-managed roles are not editable; duplicate them or create a custom role, as indicated in the page on role management.
What happens if I modify an existing role?
Changes apply to users who have this role: plan communications and test on a pilot account if the scope is broad.
Should I rely on breach cost studies to decide on roles?
Industry reports can raise awareness, but your decisions should be based on your real surface area (number of admins, apps, partners) and on Shopify documentation, not on average figures disconnected from your context.
How do I revoke access quickly?
Remove roles, disable the account, or delete the user according to your procedure; document the action in your internal ticket. For multi-store organizations, also check store access to ensure no shop remains accessible by mistake.
Require 2FA for teams
Shopify offers security settings to strengthen accounts; combine a strong password requirement, 2FA, and review of sensitive permissions for profiles that see financial data or customer exports.
Learn more

March 25, 2025